Enterprise-Grade Managed Detection and Response (MDR) Security Services
Protect your business with advanced cyber security solutions that combine enterprise-level protection with expert management. Our MDR services provide continuous monitoring, rapid threat detection, and automated response capabilities to defend your critical assets 24/7
Advanced Managed Detection and Response (MDR) Security
In today’s rapidly evolving threat landscape, traditional security measures aren’t enough to protect your business. Managed Detection and Response (MDR) provides comprehensive, proactive security that combines advanced technology with expert human analysis to defend your organization against sophisticated cyber threats.
What Makes MDR Essential for Modern Business Security
Unlike traditional security solutions, MDR services actively hunt for threats in your environment, respond to incidents in real-time, and provide expert guidance to strengthen your business's security posture.
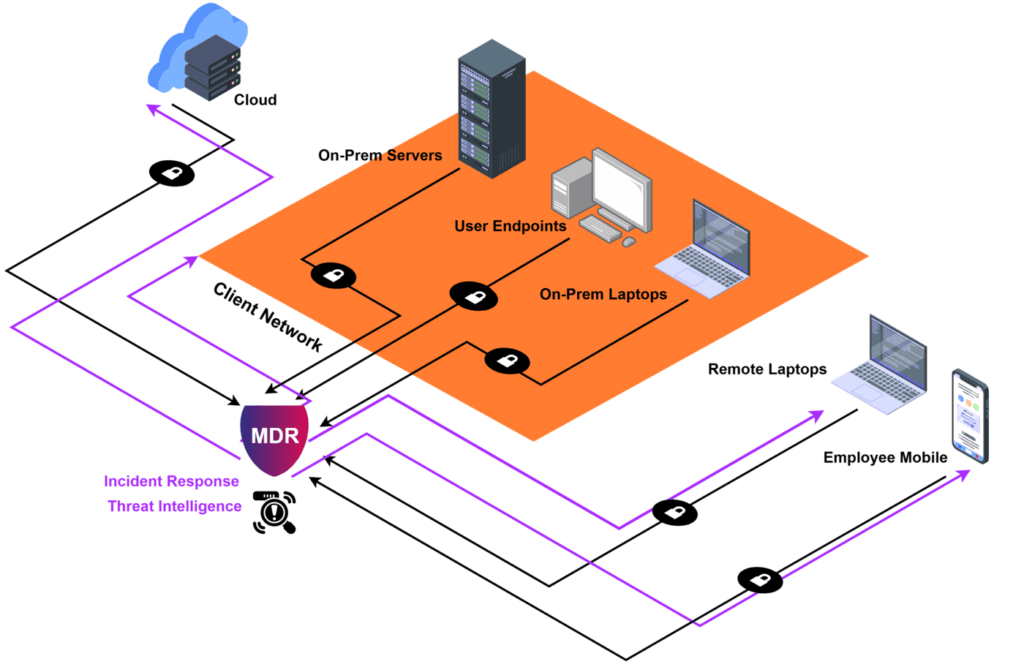
MDR goes beyond standard security monitoring by providing
Real-time threat detection using advanced AI and machine learning
24/7 monitoring by certified security analysts
Immediate automated response to contain threats
Expert investigation of security incidents
Detailed reporting and security recommendations
Continuous security posture strengthening
Key Components of Our MDR Service
Detect, respond, and protect your business with enterprise-grade security monitoring that never sleeps. Our MDR service combines advanced threat detection with expert analysis to defend your critical assets 24/7.
Continuous Threat Monitoring
Our security operations center (SOC) monitors your systems 24/7, using advanced analytics to detect suspicious activities and potential threats before they impact your business.
Automated Threat Response
When threats are detected, our systems automatically implement containment measures to prevent damage while our security experts investigate the incident.
Security Posture Improvement
Regular security assessments and detailed recommendations help strengthen your defenses against evolving cyber threats.
Industry-Specific Security Solutions
Every industry faces unique security challenges. Our managed security services are tailored to meet specific regulatory requirements and operational needs across different sectors, combining enterprise-grade protection with industry-specific expertise.
Professional Services
Advanced security solutions for consulting firms, and engineering practices. Protect intellectual property, client data, and collaborative workflows while maintaining seamless service delivery.
Financial Services
Advanced security solutions for financial institutions, including compliance with banking regulations, transaction security, and protection of sensitive customer data.
Healthcare
HIPAA-compliant security services protecting patient data and medical systems while ensuring continuous access to critical healthcare applications.
Legal Services
Comprehensive data protection ensuring client confidentiality, secure document management, and compliance with legal industry regulations.
Non-Profit Organizations
Cost-effective security solutions tailored for non-profits, protecting donor data, financial information, and mission-critical systems while maximizing your technology budget and maintaining public trust.
Mining & Resources
Robust security solutions for remote operations, protecting both site operations and corporate systems across distributed locations with reliable, always-on security.
Manufacturing
Specialized security for operational technology (OT) and IT systems, protecting production environments and intellectual property.
Warehousing & Logistics
End-to-end security for supply chain operations, protecting inventory systems, logistics data, and maintaining operational continuity.
Security Assessment and Compliance Services
Understand your security posture and meet regulatory requirements with comprehensive security assessments. Our expert team identifies vulnerabilities, ensures compliance, and provides actionable recommendations to strengthen your security framework
Security Gap Analysis
Compare your current security controls against industry best practices and compliance requirements. Receive practical recommendations for enhancing your security strategy.
Risk Analysis
Comprehensive evaluation of your security risks, threats, and business impact. Get clear insights into your security posture and detailed improvement roadmaps.
Vulnerability Assessment
Advanced scanning and testing to identify security gaps across your infrastructure, applications, and networks. Receive detailed reports with prioritized remediation steps
Compliance Management
Navigate complex regulatory requirements including HIPAA, PCI DSS, and ISO 27001. Our assessments ensure your security controls meet industry standards and compliance frameworks

Does your industry require your Business to be Cyber Security compliant?
We Follow and Implement the Requirements of all the Major Cyber Security Frameworks
The NIST Cybersecurity Framework is a set of guidelines, standards, and best practices for organizations to manage and reduce cybersecurity risks. The framework was developed by the National Institute of Standards and Technology (NIST) in response to a presidential executive order to improve critical infrastructure cyber security.
SOC 2, or System and Organization Controls 2, is a type of audit report that provides assurance on the effectiveness of an organization’s controls related to security, availability, processing integrity, confidentiality, and privacy. SOC 2 is a standard developed by the American Institute of Certified Public Accountants (AICPA) and is used to evaluate the controls and processes of service organizations that store or process sensitive data.
Take the Next Step in Securing Your Business
Your business deserves enterprise-grade security that fits your needs and budget. We’ve developed comprehensive security packages that combine our expert services, advanced technology, and proven methodologies to protect your business at every level.
Our flexible packages ensure you get the right level of protection without overpaying for features you don’t need.
Leading Cybersecurity Services in Partnership with Industry Experts
Learn more about Cyber Security and the most common types of cyber attacks in our IT knowledge blog.